Now that VMware offers an ESXi only platform in vSphere 5.0, there are logging decisions to be considered which were a non-issue on the ESX platform. Particularly with boot from SAN, boot from flash, or stateless hosts where logs can’t be stored locally on the host with no scratch partition due to not having local storage. Some shops use Splunk as a Syslog server. Other bloggers such as Simon Long have identified in the past how to send logs to the vMA appliance. Centralized management of anything is almost always a good thing and the same holds true for logging.
New in the vCenter 5.0 bundle is a Syslog server which can be integrated with vCenter 5.0. I’m going to go through the installation, configuration, and then I’ll have a look at the logs.
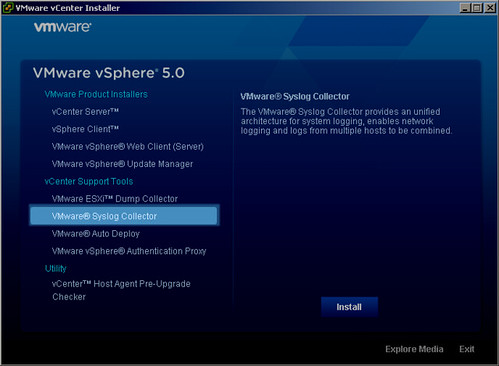
Installation couldn’t be much easier. I’ll highlight the main steps. First launch the VMware Syslog Collector installation:
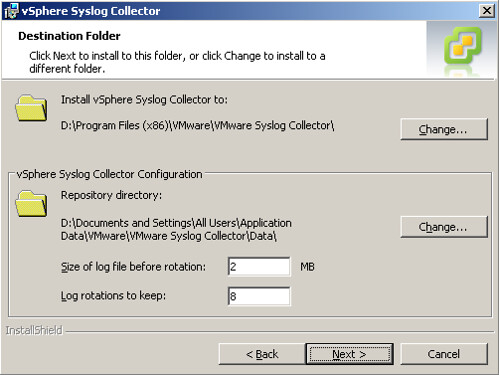
The setup routine will open Windows Firewall ports as necessary. Choose the appropriate drive letter and path installation locations. Note the second drive letter and path specifies the location of the aggregated syslog files from the hosts. Be sure there is enough space on the drive for the log files, particularly in medium to large environments:
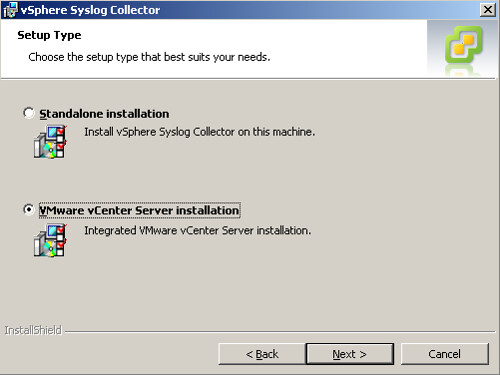
Choose the VMware vCenter Server installation (this is not the default type of installation):
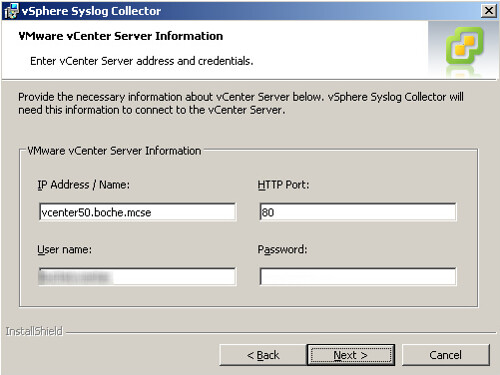
Provide the location of the vCenter Server as well as credentials to establish the connection. In this case I’m installing the Syslog server on the vCenter Server itself:
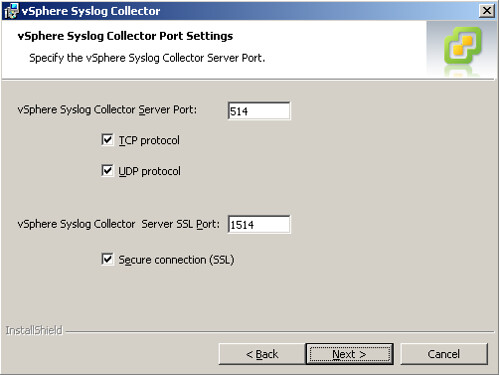
The Syslog server has the ability to accept connections on three different ports:
- UDP 514
- TCP 514
- Encrypted SSL 1514
There’s an opportunity to change the default listening ports but I’ll leave them as is, especially UDP 514 which is an industry standard port for Syslog communications:
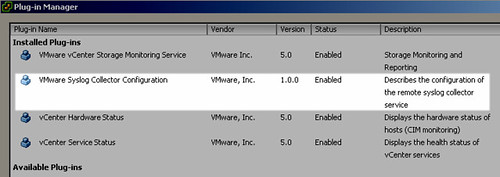
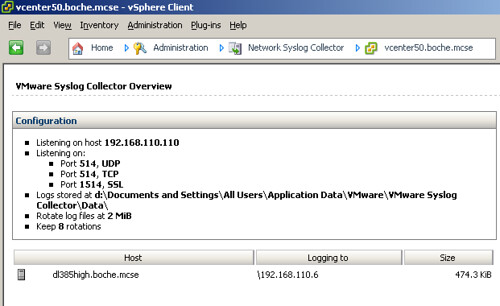
Once the installation is finished, it’s ready to accept incoming Syslog connections from hosts. You’ll notice a few new items in the vSphere Client. First is the VMware Syslog Collector Configuration plug-in:
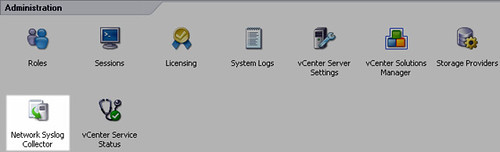
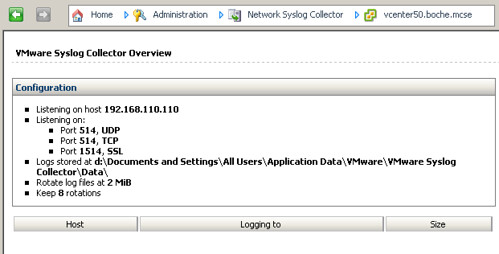
Next is the Network Syslog Collector applet:
It’s waiting for incoming Syslog connections:
Now I’ll a configure host to send its logs to the vCenter integrated Syslog server. This is fairly straightforward as well and there are a few ways to do it. I’ll identify two.
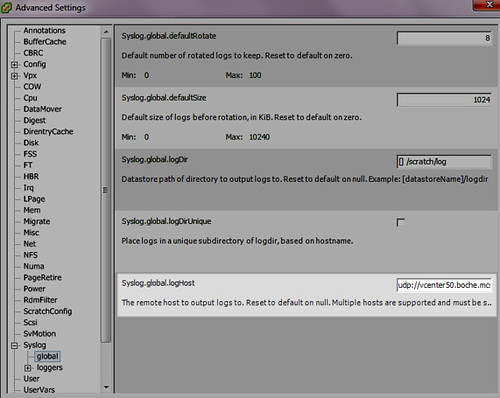
In the vCenter inventory, select the ESXi 5.0 host, navigate to the Configuration tab, then Advanced Settings under Software. Enter the Syslog server address in the field for Syslog.global.logHost. The format is <protocol>://<f.q.d.n>:port. So for my example: udp://vcenter50.boche.mcse:514. This field allows multiple Syslog protocols and endpoints separated by commas. I could write split the logs to additional Syslog server with this entry: udp://vcenter50.boche.mcse:514, splunk.boche.mcse, ssl://securesyslogs.boche.mcse:1514. In that example, logs are shipped to vcenter50.boche.mcse and splunk.boche.mcse over UDP 514, as well as to securesyslogs.boche.mcse over 1514. Another thing to point out on multiple entries.. there is a space after each comma which appears to be required for the host to interpret multiple entries properly:
There are many other Syslog loggers options which can be tuned. Have a look at them and configure your preferred logging appropriately.
Another method to configure and enable syslog on an ESXi 5 host would be to use esxcli. The commands for each host look something like this:
~ # esxcli system syslog config set –loghost=192.168.110.16
~ # esxcli system syslog reload
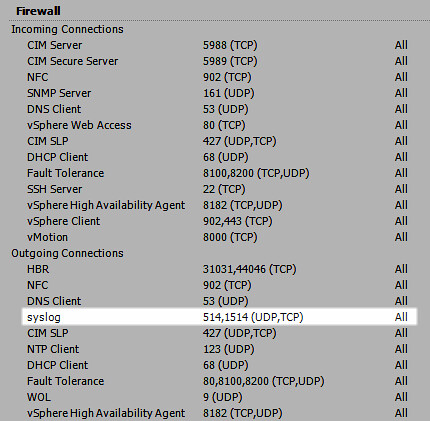
Now I’ll ensure outbound UDP 514 is opened on the ESXi 5.0 firewall. If the Syslog ports are closed, logs won’t make it to the Syslog server:
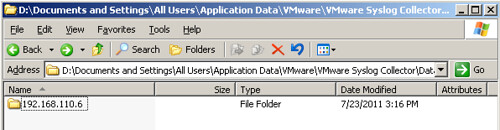
Back to the vCenter (Syslog) Server, you’ll see a folder for each host sending logs to the Syslog server:
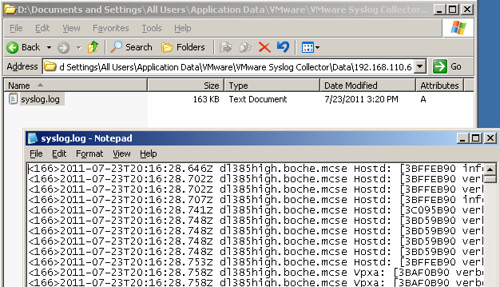
And here come the logs:
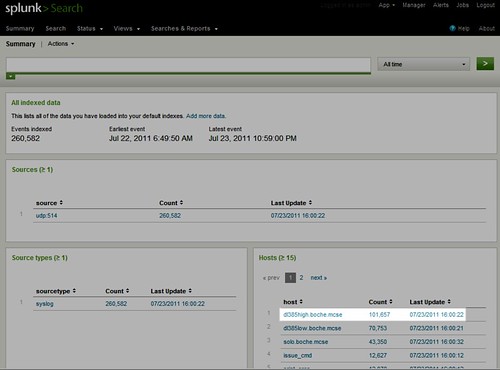
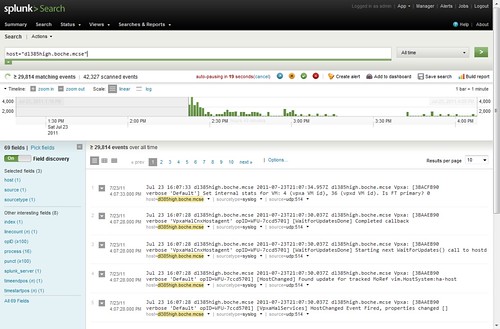
The same logs are going to the Splunk server too:
This is what the logs look like in Splunk. It’s a very powerful tool for centrally storing logs and then querying those logs using a powerful engine:
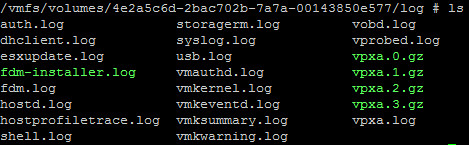
And since this host actually has local disk, and as a result a scratch partition, the logs natively go to the scratch partition:
Notice the host I configured is also displayed in the Network Syslog Collector along with the general path to the logs as well as the size of each host’s respective log file (I’ve noticed that it sometimes requires exiting the vSphere Client and logging back in before the hosts show up below):
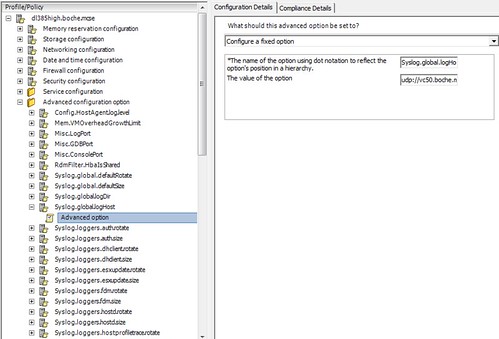
Earlier I mentioned that I’d show a second way to configure Syslog on the ESXi host. That method is much easier and comes by way of leveraging host profiles. Simply create a host profile and add the Syslog configuration to the profile. Of course this profile can be used to deploy the configuration to countless other hosts which makes it a very easy and powerful method to deploy a centralized logging configuration:
For more information, see VMware KB 2003322 Configuring syslog on ESXi 5.0.















Hi Jason
Good article, seems so simple. I am assuming here you would also add the esxi firewall ports to the host profile config for syslog?
Cheers
Great post. I see the syslog server adoption ramping up with the new AutoDeploy feature in vSphere 5.
I did not have the syslog.global.logHost entry in the host profile, had to first manually add it in advanced configuration options and then specify the vCenter server path.
Great post, thanks for sharing. Exactly what I was looking for!
It seems that the Syslogs coming from the ESXi hosts are very verbose and fill up the text files quickly. Any suggestions/instructions on how to tone these down a bit?
Thanks for sharing nice information.
I receive the following error when trying to install the Syslog
“Product: vSphere Syslog Collector — Error 29106.Unknown error.”
I am using the local admin credentials and I am able to authenticate to the vCenter server.
The account which is used during the syslog installation to register to the vCenter server should be an account which has “Register extension” privilege on the vCenter server.
This fixed the installation 🙂
Great post, thanks for sharing. Exactly what I was looking for!
It will help me to configure the VMware syslog server.