The other night I upgraded the VMware View 5.0.1 environment in the lab to 5.1 which was released on May 16th. Normally when I upgrade the View environment, I don’t actually perform an inline upgrade of the Connection Server or database. The environment is small enough that I can flatten it and rebuild fresh from scratch (including brand new VMs for the infrastructure components such as the Connection Server) for each new version VMware releases. Due to VMware’s aggressive release schedule, I also embed the production version in the infrastructure server name which helps me keep track of where things are at in the lab. Thus, with each new release, I’m building new infrastructure VMs with updated names, rather than recycling the previous infrastructure VMs, renaming them, remove/re-add to the domain, and even then I’m left with a VM name which doesn’t match the name on the datastore folder. Pushing the reset button and starting fresh obliterates any bad DNA or cooties the previous environment might have had and it gives me a little extra peace of mind when I sleep at night.
I was running a little short on time so for this round I decided to perform an inline upgrade to 5.1 rather than going through the normal rebuild routine. After all, most production environments don’t have the luxury of starting over so now was as good a time as ever to test the upgrade process of View in the lab. Again – a fairly simple setup: a Connection Server, View Composer 2.7 installed on the vCenter Server which for the first time in many releases will be upgraded to 3.0, back end databases on an external SQL server, and 3 small pools.
The View Connection Server upgrade went as planned. No issues to speak of there (yet). However, I did struggle with the View Composer upgrade. The first run through uninstalled View Composer and failed with an error which I wasn’t quick enough to capture. I re-ran through the Composer installation and it failed again with the same error:
The wizard was interrupted before VMware View Composer could be completely installed.
While I was perfrming some troubleshooting, a couple of gracious folks on Twitter by the name of Diego Quintana and Tim Washburn (@daquintana and @mittim12 respectively) pointed out VMware KB article 2017773 Installing or upgrading View Composer fails with error: The wizard was interrupted before VMware View Composer could be completely installed which resolved my issue. The previous View Composer installation had placed one or more keys in the directory C:\ProgramData\Microsoft\Crypto\RSA\MachineKeys\ which my user account no longer had NTFS permissions to. The resolution was to simply relax the NTFS permissions both on the MachineKeys folder as well as the files inside of the folder for good measure.
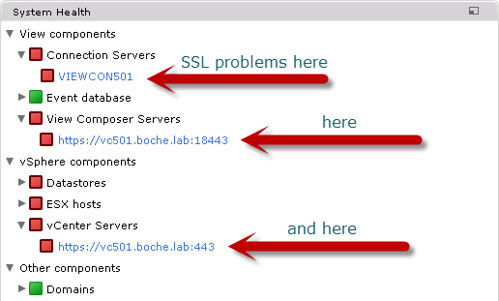
I thought I was out of the woods, but not quite yet. SSL certificate issues followed.
VMware made some new changes with regards to SSL in View 5.1 which are documented at <View installation drive letter>:\Program Files\VMware\VMware View\Server\README.rtf
Copied and pasted verbatim, the release notes are:
Read These Notes! Your View 5.1 Setup Will Be Easier!
You can read these notes in your language:
Français Deutsch 简体中文 日本語 한국어
We made changes in View 5.1 that require you to configure View components a little differently than in the past. These notes will help you to avoid potential pitfalls when you install or upgrade to View 5.1.
1) You cannot downgrade View 5.1 Connection Server to previous versions.
In View 5.1, the View LDAP configuration is encrypted and cannot be used by earlier versions of View.
- After you upgrade a View Connection Server instance to View 5.1, you cannot downgrade that instance to an earlier version.
- After you upgrade all View Connection Server instances in a replicated group, you cannot add another instance that runs an earlier version of View.
Note: Downgrading was never supported, but in past releases it worked. Now it won’t work.
2) vCenter Server and View Composer hosts need valid SSL certificates.
- Best choice: Ensure your vCenter Server and View Composer have Certificate Authority (CA)-provided certificates:
o Install an SSL certificate, signed by a CA, on the Windows Server on which vCenter Server is installed.
o Do the same for View Composer. If you install View Composer and vCenter Server on the same host, they can use the same certificate, but you must configure the certificate separately for each component.
* If you install the certificate before you install View Composer, you can select your certificate during the View Composer installation.
* If you replace the default certificate later, run the SviConfig ReplaceCertificate command to bind the new certificate to the port used by View Composer.
o Make sure the CA for the new certificates, and any parent CAs, are trusted by each Windows server on which a View Connection Server instance is installed.
- Alternative: After you add vCenter Server and View Composer to View, accept the thumbprint of the default certificate for View Composer by clicking Verify in View Administrator. Do the same for vCenter Server.
More information: See “Configuring SSL Certificates for View Servers” in the View Installation guide.
3) Security server and View Connection Server hosts need valid SSL certificates.
- Best choice: After you install a View Connection Server instance or security server on a Windows Server host, open the Windows Server certificate store and take these steps:
o Import an SSL certificate that is signed by a CA and that your clients can validate.
o Make sure that the entire certificate chain, including intermediate certificates and root certificate, are installed.
o Make sure the certificate has a private key, and mark the key as exportable.
o Configure the certificate Friendly Name as vdm.
- Alternative: Let the View server installer create a default certificate in the Windows Server certificate store. The certificate is self-signed and will be shown as invalid in View Administrator.
- Upgrading to View 5.1: If your original View servers already have SSL certificates signed by a CA, you don’t have to do anything. During the upgrade, View imports your certificates into the Windows Server certificate store.
If your original View servers have default certificates, upgrade your View servers and follow the Best choice steps shown above.
More information: See “Configuring SSL Certificates for View Servers” in the View Installation guide.
4) Certificates for vCenter Server, View Composer, and View servers must include certificate revocation lists (CRLs).
View will not validate a certificate without a CRL.
- Best Choice: lf needed, take these steps:
o Add a CRL to your certificate.
o Import the updated certificate into the Windows certificate store on the vCenter Server, View Composer, and View server host.
- Alternative: Change the registry settings that control CRL checking.
More information: “Configuring Certificate Revocation Checking on Server Certificates” in the View Installation guide.
5) Windows Firewall with Advanced Security must be enabled on Security Server and View Connection Server hosts.
By default, IPsec rules govern connections between the View security server and View Connection Server and require Windows Firewall with Advanced Security to be enabled.
- Best choice: Set Windows Firewall with Advanced Security to on before you install the View servers. Make sure it’s on for any active profiles; better still, set it to on for all profiles.
- Alternative: Before you install security servers, open View Administrator and disable the Global Setting, Use IPsec for Security Server Connections, by setting it to no. (This is not recommended.)
6) Back-end firewalls must be set up to support IPsec.
If you have a back-end firewall between security servers and View Connection Server instances, you must configure firewall rules to allow the connections to work.
More information: See “Configuring a Back-End Firewall to Support IPsec ” in the View Installation guide.
7) View Clients must use HTTPS to connect to View.
View Connection Server instances and security servers use SSL for client connections.
- If View clients connect via an SSL off-loading intermediate device, you must install the intermediate device’s SSL certificate on View Connection Server or security server.
- The connection must be HTTPS whether or not a View client connects via an intermediate device such as a load balancer. If you use an intermediate device, and you want the connection between the intermediate device and View server to be over HTTP (SSL off-loading), configure the locked.properties file on the View server.
- Older View clients that can choose not to use HTTPS will get an error if users select HTTP. Previously they were silently redirected to HTTPS. Clients that cannot make SSL connections will be unable to connect to View.
More information: See “Off-loading SSL Connections to Intermediate Servers” in the View Administration guide.
8) Encrypted and cleansed View backups require new restore steps.
By default, View 5.1 backups are encrypted. You can also cleanse View backups (exclude passwords and other sensitive information from the backup data) or back up in plain text (not recommended).
- To restore an encrypted backup, you must decrypt the data first. You must use the data recovery password that you provided when you installed View Connection Server.
- Do not restore cleansed backups. Data such as passwords will be missing from your View LDAP configuration. View components will not function properly without this data. To restore normal functionality, you will have to use View Administrator to manually reset all passwords and other missing data items.
More information: See “Backing Up and Restoring View Configuration Data” in the View Administration guide.
9) Before you can upgrade or reinstall a View 5.1 security server, you must remove the relevant IPsec rules from the paired View Connection Server instance so that fresh rules can be established.
- In View Administrator, select the security server and click More Commands > Prepare for Upgrade or Reinstallation.
Note: You don’t need to remove a security server from View before you upgrade or reinstall the server.
More information: See “Prepare to Upgrade or Reinstall a Security Server” in the View Installation guide.
Ok, so basically VMware is pushing for the use of SSL certificates from a trusted CA whether that be externally (VeriSign, etc.) or internally (Microsoft Certificate Services) generated. For the time being, I have ditched my internal Microsoft CA and wish to continue using the self signed certificates shipped and installed by View. To do so, as explained in the README above, one must visit the System Health in the View Administrator Dashboard and verify the certificates for the vCenter Server as well as the View Composer Server (each will be seen in a red status in the dashboard). The Connection Server certificate cannot be verified and will remain in a red status however from this point forward both the View Connection Server and View Composer will function normally.
Upgrading the View Agents and recomposing the pools was a non-issue and the upgrade was completed successfully. After all is said and done, the environment is working and the upgrade was successful. View 5.0.1 Clients have no problem connecting to the new 5.1 environment; I’ll get the clients upgraded in the near future and I’ll consider resurrecting the lab CA to generate trusted SSL certificates.















Great post!
Do you know to reference or bypass the certificates in silent installation? Thanks!
Steve
I just wanted to jump in in on this thread. I know people in general have difficulty when implementing ssl certs for openssl, so I looked around and found a ssl tool that makes installation of ssl certs on cpanel a snap. Check it out at http://tools.ssl.com. Happy trails with your ssl installations!